The below short bit of PowerShell is helpful to find computers that have not communicated to an Active Directory domain controller in a definable number of days. The beauty of using PowerShell is you don’t need any third party software, and it is free.
Generally if a computer is no longer talking to the domain it would mean the computer account is now obsolete, maybe because the computers has been lost, stolen or otherwise disposed. It could also be a computer in a branch office that can’t communicate with the domain controller because of some sort of network issue.
In any case the following PowerShell will help you to audit computer accounts that are no longer in use, or communicating back to Active Directory.
You will need to have the RSAT tools installed, see my post Install all RSAT tools via PowerShell for a quick and simple method of them if required.
You will also need to be logged on with a domain user account and be able to communicate with a domain controller. You could also run this script from a domain controller.
- $ComputerPasswordAgeDays = 90 sets the number of days, i.e show computers that have not communicated in 90+ days. Change as needed
- -and (OperatingSystem -notlike “Server“) filters out servers OS’s from the results. Remove if you want to include servers
- -and (OperatingSystem -like “Windows“) Filters for just Windows clients, I have a few Mac OS computers on my domain. Remove if you want to include non Windows joined computers
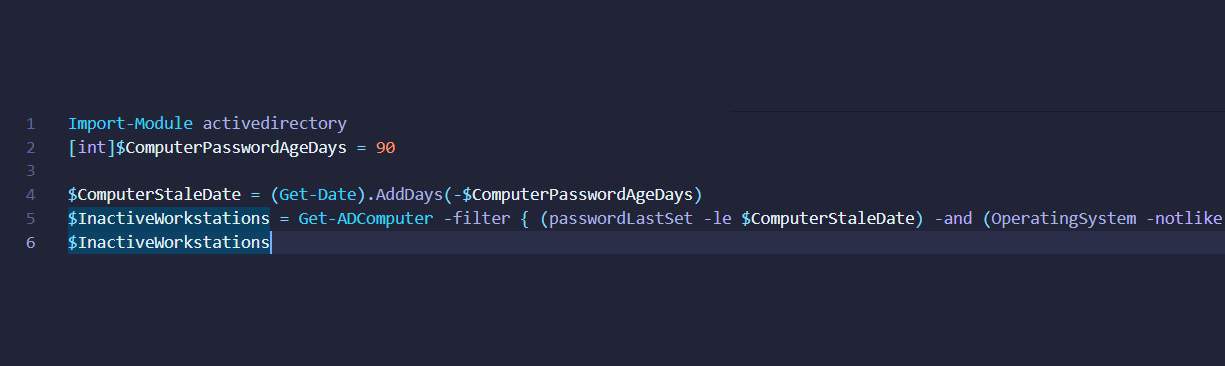
Import-Module ActiveDirectory
[int]$ComputerPasswordAgeDays = 90
$ComputerStaleDate = (Get-Date).AddDays(-$ComputerPasswordAgeDays)
$InactiveWorkstations = Get-ADComputer -filter { (passwordLastSet -le $ComputerStaleDate) -and (OperatingSystem -notlike "*Server*") -and (OperatingSystem -like "*Windows*") } -properties Name, DistinguishedName, OperatingSystem,OperatingSystemServicePack, passwordLastSet,LastLogonDate,Description
$InactiveWorkstations
- If you would like to export to CSV change the last line to
$InactiveWorkstations | export-csv "C:\folder\filename.csv"